- February 25, 2026
- by Anoop Jain
Kubernetes, CI/CD, and Cloud Security: Staffing Modern Cloud Teams the gNxt Way
Modern cloud engineering is no longer about lifting and shifting applications to virtual machines. True cloud readiness — one that delivers continuous innovation, enterprise resilience, and secure deployments — demands a blend of container orchestration (primarily Kubernetes), automated delivery (CI/CD), and security integrated at every stage of the delivery lifecycle.
As organizations transition to cloud-native platforms, they increasingly realize that technology alone does not guarantee success. What separates high-performance teams from average ones is the quality of personnel, the engineering processes they adopt, and the governance practices that support them.
In India — one of the most active global hubs for cloud talent — enterprises often struggle to source and retain teams capable of simultaneously mastering Kubernetes, CI/CD pipelines, and cloud security. The gap is not just technical. It’s strategic.
This blog explores the institutional challenges in staffing modern cloud teams, the real engineering practices that make cloud initiatives successful, and how gNxt Systems uniquely positions enterprises to build resilient, scalable cloud delivery teams with operational excellence.
Why Kubernetes Has Become the Backbone of Cloud Native Engineering
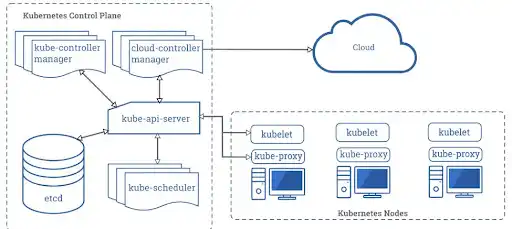
Kubernetes has evolved from a niche container orchestration tool to the central nervous system of modern cloud infrastructure. It enables enterprises to manage containerized workloads with declarations, automation, and resiliency across hybrid and multi-cloud environments. Kubernetes abstracts infrastructure differences and delivers highly available, self-healing systems — a vital requirement for businesses that expect continuous uptime and seamless scalability.
Beyond deployment automation, Kubernetes enables strategic capabilities such as rolling updates, service discovery, dynamic scaling, and workload isolation — all critical for mission-critical applications that serve global traffic. Its rapid adoption is evidenced by industry usage surveys and its long ecosystem of tools and managed services (e.g., AWS EKS, Azure AKS, Google GKE).
However, Kubernetes’ power comes with complexity. Teams must understand cluster architecture, declarative configuration models, and how workloads behave under different failure modes. Without this expertise, enterprises face fragmented infrastructure management, unstable deployments, and technical debt — all of which slow down innovation.
The Role of CI/CD in Enabling Cloud-Native Delivery
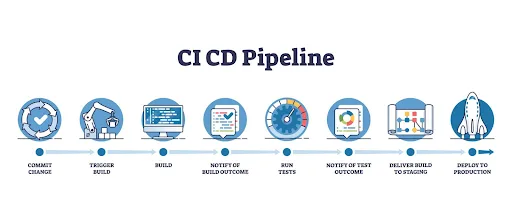
While Kubernetes manages how applications run, Continuous Integration and Continuous Delivery (CI/CD) determines how applications are built, tested, and delivered. At its core, CI/CD automates the journey of code from a developer’s workstation into production — enabling frequent, reliable releases.
CI focuses on automated building and testing of code changes, reducing integration friction by validating changes each time new code is committed. CD extends this by automating the release of validated changes into staging or production environments, often without manual intervention.
In cloud-native environments, CI/CD pipelines integrate with Kubernetes to automate application delivery. Popular tools such as Jenkins, GitHub Actions, GitLab CI/CD, ArgoCD, and Flux enable teams to automate everything from container image building to deployment, rollout strategies (like blue-green), and rollback procedures. Using CI/CD with Kubernetes makes delivery processes reproducible, observable, and faster — reducing lead times and boosting engineering velocity.
Cloud Security: Beyond Perimeter Protection
As organizations adopt cloud platforms and containerized workloads, traditional security approaches — focused on network perimeters — are inadequate. Modern cloud security demands a Zero Trust mindset and DevSecOps practices that embed security into every stage of delivery.
Cloud workloads expose a broader attack surface, including API endpoints, container images, orchestration layers, and CI/CD systems themselves. Attackers increasingly target weak IAM policies, insecure container images, misconfigured network policies, and unmonitored runtime behavior. Protecting this landscape requires identity safeguards, automated compliance checks, and continuous threat detection integrated into deployment pipelines.
Integrating security into the CI/CD process is no longer optional. Security scans, policy enforcement, secrets management, container image scanning, and runtime threat detection must occur automatically within pipelines. This DevSecOps approach ensures that security policies are enforced before code ever reaches production — significantly reducing operational risk.
Staffing Challenges in Modern Cloud Engineering
Despite the clear technological priorities, many enterprises struggle to staff cloud engineering teams effectively. Traditional hiring processes often treat Kubernetes engineering, CI/CD automation, and cloud security as individual skill silos rather than parts of a cohesive delivery capability. This leads to teams that excel in one domain but lack the cross-functional expertise to deliver secure, scalable systems end-to-end.
Moreover, cloud engineering demands proficiency across a range of tools and practices: infrastructure as code (IaC), configuration management, monitoring, observability, policy-as-code, and multi-cluster management — all requiring not only technical skills but also practical experience in interpreting and enforcing governance at scale.
Attracting and retaining such talent is increasingly competitive, especially as digital transformation initiatives accelerate. Enterprises can no longer rely solely on campus hiring or ad hoc contractor models; they need strategic staffing solutions that embed talent with the right mix of cloud engineering expertise and operational maturity.
How gNxt Systems Builds Modern Cloud Delivery Teams
At gNxt Systems, we treat staffing as an enterprise capability service, not a transactional hiring activity. Rather than providing isolated specialists, we design and deliver integrated cloud teams aligned with business outcomes and technical maturity.
Our teams are structured around operational disciplines:
- Kubernetes architects with experience in production deployments and multi-cluster management
- CI/CD automation engineers who design pipelines for scalability and reliability
- Cloud security engineers who embed DevSecOps controls into delivery workflows
- Site Reliability Engineers (SREs) who ensure uptime, observability, and resilience
- Platform engineers who build internal developer platforms and automation tooling
This model ensures teams do not act as isolated contributors but as cohesive units that deliver secure, dependable cloud workloads.
By aligning staffing to modern cloud delivery practices and enterprise governance expectations, gNxt Systems helps organizations reduce deployment failures, strengthen operational security, and accelerate time-to-market.
Trends Shaping Cloud Engineering in 2026 and Beyond
Looking ahead, several trends are reshaping cloud engineering:
Zero Trust Security is becoming standard practice, requiring every access request — internal or external — to be authenticated and validated continuously. Cloud teams must adapt by integrating identity security, policy enforcement, and real-time monitoring into their workflows.
GitOps — a paradigm that uses Git as the single source of truth for infrastructure and deployment states — is gaining traction as a reliable way to standardize deployments and enable auditability.
Infrastructure as Code (IaC) continues to rise, enabling teams to manage configurations declaratively and ensure reproducibility across environments.
Multi-cluster and hybrid cloud strategies are increasingly adopted to optimize performance, manage cost, and satisfy regulatory requirements.
Real Enterprise Insight: CI/CD Security Is a Growing Priority
Integrating security directly into CI/CD pipelines — often described as DevSecOps — is now essential to prevent vulnerabilities from reaching production systems. Security must be automated within the pipeline, including secret handling, code scanning, dependency checks, and policy validations.
Without such integration, organizations risk exposing sensitive data through pipeline tools themselves, as CI/CD systems often contain access credentials, logs, and deployment scripts — making them attractive targets for sophisticated attacks.
Modern enterprises that treat security as part of the delivery process rather than a separate phase have better delivery outcomes, fewer breaches, and stronger compliance postures.
Q1. What is Kubernetes and why is it important for cloud engineering?
Q2. What is the difference between Continuous Integration and Continuous Delivery?
Q3. How does cloud security integrate into CI/CD pipelines?
Q4. What are common challenges when staffing Kubernetes and CI/CD teams?
Q5. Why is zero trust architecture becoming critical in cloud security?
About Author
CEO at gNxt Systems
with 25+ years of expertise, Mr. Anoop Jain delivers complex projects, driving innovation through IT strategies and inspiring teams to achieve milestones in a competitive, technology-driven landscape.